Communicate in HTTPS from end to end
Establish HTTPS redirection and HSTS for your final users
Ideally, enable Force HTTPS in your site configuration on Ogo.
Final users will communicate with Ogo in a secure mode: their transactions will be encrypted and confidential and Ogo's identity will be verified.
In addition, use HSTS to prevent Man-In-The-Middle attacks.
Communicating in HTTPS between Ogo and your server
It is recommended to switch the Protocol between OGO and your origin server to HTTPS in the configuration of your site on Ogo.
However, this requires that your server has a certificate. If it doesn't, you can get one fairly quickly by purchasing/generating one from a certificate authority.
This setting ensures the confidentiality of transactions between Ogo and your server on the Internet.
Maintain and verify your original certificate
Finally, you must deactivate Never check origin server certificate.
To do this, you will need to maintain your server's certificate in a valid state.
This setting will allow Ogo to verify the identity of your server, preventing MITM attacks.
Only allow traffic from Ogo
On the traffic arriving at your server, you should only allow traffic from Ogo.
Allow only traffic from OGO
Solution 1: Restrict to our outbound IPs
For incoming traffic to your server, only allow traffic originating from OGO’s outbound IPs.
Solution 2: mTLS (recommended)
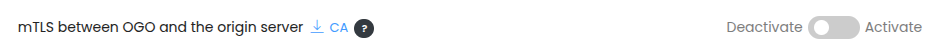
On your server, upload the OGO Certificate Authority and only accept incoming traffic from clients presenting a certificate issued by this authority.
You can download the OGO Certificate Authority and enable this mode in the site configuration: